DoS - Mr. Pixel Flood
Summary :
Denial of Service (DoS) attacks have a poor reputation. Historically, DoS used to be trivial you could knock most sites offline using script-kiddie friendly tools like slowloris.pl. DoS attacks are also often conflated with DDoS attacks, which are near-impossible to truly fix. A line was drawn between a site being ‘hacked’, and merely being (D)DoS’d. As a result many hackers, regarded DoS vulnerabilities as lame.
Today I’ll show you a good technique to get bounty using DoS. So there are many ways to create a Denial-Of-Service attack but most of them end up as Informative or N/A. So their is an effective technique in which an image is uploaded in the profile photo that has the maximum pixel size of 64250px and gives you the time out, creating a DoS.
How to find this vulnerability ?
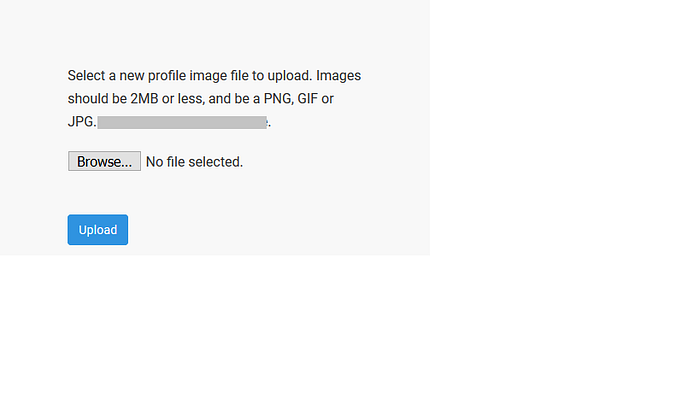
- Go to your target website and upload a profile photo
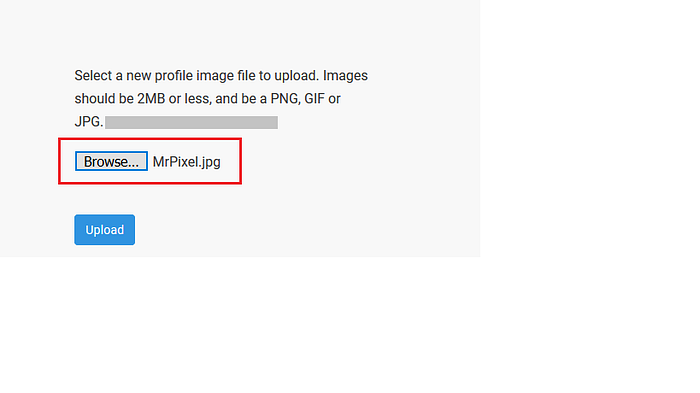
2. The photo should have the pixel size of 64250*64250px (height and width)
3. Select the file and upload it
3. After uploading just check the response you’ll get a timeout error
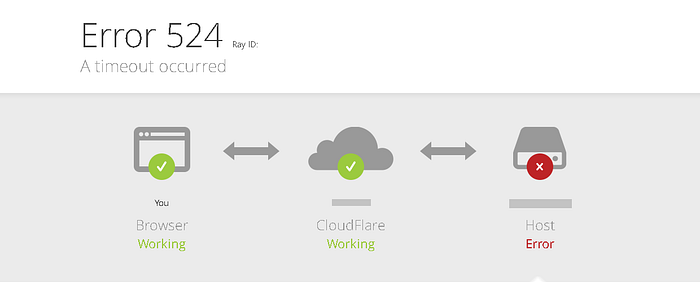
Here the service is trying to convert the image once uploaded, by loading the ‘whole image’ into memory. It tries to allocate 4128062500 pixels into memory, flooding the memory and causing DoS.
In some cases the website doesn’t allow you to upload the 64250*64250px images due to security, so you need to bypass it. Bypassing is very simple just replace the 64250*64250px value with 0xfafa*0xfafa this is equivalent to 64250 in Decimal number system and it’s binary format is 1111101011111010.
I would like to share one more thing, it is not only related to profile photo upload, you can try uploading it where ever you find the photo upload option.
You can make your own image here : https://www.resizepixel.com/
NOTE : I do have the MrPixel image if you want just DM me your email on my instagram.
Thank You :)
Instagram : jerry._.3
